 If you happen to get this phone in your hands you probably are expecting more than making calls and texting. And you quite possibly already know that Android is based on Linux in a way, which ignites your curiosity even more. Here are a few steps you might consider to enhance your device’s potential at the very beginning of your experience.
If you happen to get this phone in your hands you probably are expecting more than making calls and texting. And you quite possibly already know that Android is based on Linux in a way, which ignites your curiosity even more. Here are a few steps you might consider to enhance your device’s potential at the very beginning of your experience.
Just to be clear – I do not take responsibility of any unpredictable results rendered by actions provided below. In other words – if you break your device I am not to blame. Use with caution, these come without any warranty, even implied warranty of fitness for a particular purpose 🙂
1. Charge it fully, then let it drain the battery until it dies, and then recharge again
There are a lot of myths regarding battery formatting, but just to be on the safe side my recommendation is to just do it. Let’s face it – this is a smartphone and it will be draining your battery a lot as you play with it and/or configure idle activities such as changing wifi sleep or wifi scanning period, etc. Therefore keep your battery in shape.
2. Mind your warranty and note down vital components’ versions
![]() Techniques and steps described below will make your warranty questionable. There are various opinions on the Internet regarding what voids it and what does not. Changing phone software, rooting it, changing recovery partition – certainly do. Carefully consider your rollback plan if you need to. If you search the net you might get original Samsung kernel to reflash it, possibly same applies to the ROM (the userspace system actually is confusingly nicknamed as ROM), not sure about recovery component though. YMMV.
Techniques and steps described below will make your warranty questionable. There are various opinions on the Internet regarding what voids it and what does not. Changing phone software, rooting it, changing recovery partition – certainly do. Carefully consider your rollback plan if you need to. If you search the net you might get original Samsung kernel to reflash it, possibly same applies to the ROM (the userspace system actually is confusingly nicknamed as ROM), not sure about recovery component though. YMMV.
Note down your components’ versions. Home -> Menu -> Settings -> About. What matters are four items at the end (Android OS version, Baseband version, Kernel version and Version Number – the userspace).
My current setup (non-standard!):
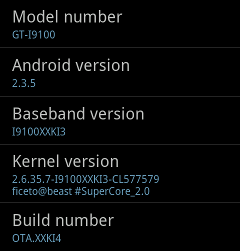
Original Samsung data is certainly different.
3. Get Android SDK with adb (Android Debug Bridge) and get heimdall
If you are running on Windows – just search for it, download and install your usual way. You should also set-up Kies drivers in Windows – as far as I have heard you will need this for adb and/or flashing.
If you are running Linux – search for android sdk within your distribution first. On Gentoo:
emerge dev-util/android-sdk-update-manager
Run “android” and update/download Android SDK Tools and Android SDK Platform-tools at least. The latter contains the excellent adb.
Plug in your phone via USB and try the following for your first impression:
$ adb shell uname -a $ adb shell cat /proc/cpuinfo
You can also push/pull files/directories with recursion to/from phone. See adb‘s help for reference.
Glass Echidna will provide you with Heimdall. Windows people will use Odin. These are the tools for flashing your phone from your PC while the phone is in download mode (phone OS not running) – more on that follows.
Flashing with these increases flash counter in the phone, which is visible to service personnel if you bring it to a service centre for repairs. There is a way to reset the counter though, but I did not try this on my own playground.
4. Root it.
This is the very beginning – it will allow you to do most of stuff from within the running system. This also opens up possibilities for advanced software you might install further down the line – like backup utilities for example. This will also allow you to render your phone completely unusable if used without care (rootprompt assumes you know and understand the meaning of its ^root prefix).
Android world provides plenty of ways and instructions to do it for most hardware implementations. I will cover two general approaches here – one is a userspace exploit 🙂 and the other is flashing a custom kernel (which as far as I guess provides installation of su binary from built-in initrd/initrams image, but still is a “foreign” kernel).
Rooting by exploiting
It has one advantage – the kernel is left untouched. It involves getting and unpacking the toolkit and running commands in the script provided (on your PC). These push files, run them, suid the su, etc. The vital part is what the exploit does; output from my run follows:
$ adb shell "./data/local/tmp/zergRush" [**] Zerg rush - Android 2.2/2.3 local root [**] (C) 2011 Revolutionary. All rights reserved. [**] Parts of code from Gingerbreak, (C) 2010-2011 The Android Exploid Crew.[+] Found a GingerBread ! 0x0002b118 [+] Found a Samsung, running Samsung mode [*] Scooting ... [*] Sleeping a bit (~40s)... [*] Waking ! [*] Sending 149 zerglings ... [+] Zerglings found a way to enter ! 0x10 [+] Overseer found a path ! 0x0002d4b8 [*] Sleeping a bit (~40s)... [*] Waking ! [*] Sending 149 zerglings ... [+] Overseer found a path ! 0x0002d7a0 [*] Sleeping a bit (~40s)... [*] Waking ! [*] Sending 149 zerglings ... [+] Zerglings caused crash (good news): 0x40322cd4 0x0054 [*] Researching Metabolic Boost ... [+] Speedlings on the go ! 0xafd1963b 0xafd3933f [*] Sleeping a bit (~40s)... [*] Waking ! [*] Popping 24 more zerglings [*] Sending 173 zerglings ...[+] Rush did it ! It's a GG, man ! [+] Killing ADB and restarting as root... enjoy!
After the reboot:
$ adb shell su -c id uid=0(root) gid=0(root)
Note that busybox is present there too, compare
$ adb shell ls -al
with
$ adb shell busybox ls -al
Rooting by a custom kernel
This method is a bit more invasive. Moreover, a non-Samsung kernel flashed externally will trigger a yellow warning triangle on the first boot screen – this can be taken care of later. You need to find the specific CF-root image for your device and current software version to minimize the risk of something going wrong. There is an excellent thread on XDA forums to help. Before you proceed with flashing it look up and get the original Samsung kernel – again, matching your software. You might need it in case anything goes wrong and certainly will need it in for one additional (but optional) step below.
The key component is Heimdall here, so make sure it runs on your system and displays the help text.
Unpack the zip to get the familiar zImage file. Boot the phone into download mode: hold volume down button and home button while switching on the phone. The upload command:
# heimdall flash --kernel zImage
After a few seconds – enjoy your rooted phone; note also the CWM Manager installed in your Applications.
The yellow triangle is neither elegant nor relaxing. To get rid of this issue the kernel needs to be loaded from inside the OS, first having the original Samsung kernel flashed to reset the current situation. The su and other tools are already in place, therefore flashing Samsung kernel for a minute will not revert that.
Get your zImage files and push these to /scard/ with meaningful names, eg. samsung.zImage and cfroot.zImage (the .zImage is mandatory for some flashing applications). samsung.zImage is not required in /sdcard/, however it might come handy every now and then.
Boot into download mode – for example with:
$ adb reboot download
and flash the Samsung kernel. After successful boot run CWM Manager on the phone. From within the application flash the cfroot.zImage kernel.
Enjoy the deep blackness in place of the yellow triangle.
5. Install CWM Recovery (if not already installed with CF-root)
This usually comes packaged with a custom kernel if provided by vendor. Most custom ROMs provide it, and so CF-root kernel does.
6. Backup your /efs directory
This directory contains vital information about you phone, including IMEI data. Do not tamper with it in any way. Grab the adb shell and tar/gzip the directory, then pull it to your PC. You might also dd the block device where it gets mounted from.
If you just did this you probably have noticed that / is mounted read-only. Be cautious with remounting it read-write; there is writeable /data filesystem available, so mkdir /data/tmpstuff and write there.
7. Backup your current ROM
Hold the power button and notice additional options. Choose Recovery to boot the recovery component. Or:
$ adb reboot recovery
The options provided are pretty self-explanatory. Your backup will be stored at /sdcard/clockworkmod/ – just pull it after you reboot the system.
8. Optionally flash a custom ROM of your choice (potential data wipe)
Choosing a custom ROM is a matter of balance between taste, hardware support, stability and features required. Personally I am currently running DarkyROM2 XXKI4 with all its pros and cons. The XXKI3 for example has a nice percentage display of battery level, however the XXKI4 lacks it currently but is based on Android 2.3.5 release. Read the instructions carefully, some ROM packages require and will wipe your user data. That’s why it’s one of “first things first”.
9. Touch the Android to continue 🙂
Enjoy your system. Make sure you have Superuser application installed – it is responsible for su rights for other applications.
10. Tools – rootprompt‘s highlights
In order to avoid bloating this already long enough article I will just summarize some applications which rootprompt‘s reader may find useful:
![]() Tasker – the swiss army knife for phone automation. Define an event (such as: phone ringing, SMS received, wifi X in range, device boot, your location…) and specify a task list to be executed (play something, display a message, run an application, bring up configuration, blink, say something, run anything else…). Vibrate shortly when my wifi is in range. When car kit is disconnected save my current location, then tap icon to navigate to stored location – use case: where did I leave my car on the parking lot? Worth much more than it’s price.
Tasker – the swiss army knife for phone automation. Define an event (such as: phone ringing, SMS received, wifi X in range, device boot, your location…) and specify a task list to be executed (play something, display a message, run an application, bring up configuration, blink, say something, run anything else…). Vibrate shortly when my wifi is in range. When car kit is disconnected save my current location, then tap icon to navigate to stored location – use case: where did I leave my car on the parking lot? Worth much more than it’s price.
![]() BLN control – with SuperCore_2.0 kernel you get support for LED API. The Samsung Galaxy S2 does not have an indicator led so it uses the Menu and Back backlight for that. This application lets you set-up a few options related to this. There is also a paid Pro version.
BLN control – with SuperCore_2.0 kernel you get support for LED API. The Samsung Galaxy S2 does not have an indicator led so it uses the Menu and Back backlight for that. This application lets you set-up a few options related to this. There is also a paid Pro version.
![]() Locale Execute Plugin – lets you run any underlying Linux command from Tasker – there are endless uses for that as you imagine. Edit: there is an alternative: Secure Settings – runs the commands faster, and allows a few more actions 😉
Locale Execute Plugin – lets you run any underlying Linux command from Tasker – there are endless uses for that as you imagine. Edit: there is an alternative: Secure Settings – runs the commands faster, and allows a few more actions 😉
![]() Titanium Backup root – a great tool to back up your applications, the user data, among other features. The paid version can also “freeze” an application – back it up and remove. This comes helpful with one particular unlock bug 😉
Titanium Backup root – a great tool to back up your applications, the user data, among other features. The paid version can also “freeze” an application – back it up and remove. This comes helpful with one particular unlock bug 😉
Gentoo – yes, I have it installed – but this is a topic for another article…
Good luck!
Related articles
- http://forum.xda-developers.com/showthread.php?t=1125282
- Gentoo on Samsung Galaxy S2 (rootprompt.apatsch.net)
- Gentoo on Android – cross compilation with distcc (rootprompt.apatsch.net)
Woah this weblog is fantastic i really like reading your posts. Keep up the great work! You know, lots of people are looking round for this information, you can help them greatly.